Hi folks,
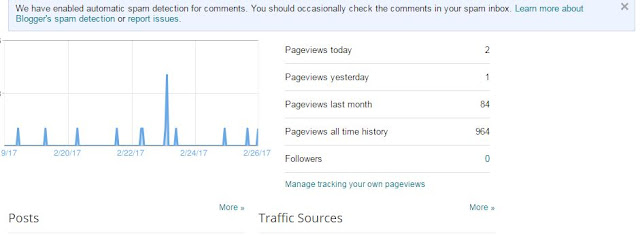
Firstly I would like to thank all the viewers of my blog. I have 964 hits so far. I got 7 feedback via email so far (all productive). Thanks especially to Sysinternals forum, Stack overflow and Linkedin. I will try to incorporate most of the things requested in the feedback. So keep sending your comments to gnomicbits@gmail.com or comment to the posts.
Today's post is more on windows security. It is especially useful for programmers who write anti-malware applications (beginners) or who want to understand the internals of some of them. I found it really difficult to find an appropriate title but finally gathered few words.
While I could have written the code in 'C' or 'C++' I wanted to thank Hutchison and Four-F and I didn't find a better way to do that. The "innovation" around reduction of "development-kit" size is quite appreciable. Secondly Four-F kit is simply incredible. It also includes undoc headers. Together MASM (and assembly language know-how) and Four-F's KMD kit is a must for any security professional especially System Hacking (coding). It also would be the first steps to going for other versions of "ASM" that provide 64-bit support.
Although I haven't studied differences between "undocumented API" available in the Four-F kit and Alex's NDK, completely, I still think it would be a value-add to convert the NDK to ".INC". Something I am working on... I know these are almost history but isn't that also important for Malware Analysts :) - they will agree.
So today I wanted to talk about three very important and elegant SPI (SPI = System programming interface. SPI < > API), that windows has been providing since Windows 2000. I will put focus on Windows 2000 (like most other posts of this blog) but it is still applicable to later versions and I will try to add enough information about changes in newer OS version.
So the 3 functions that I would prefer to call as "SPI" but are categorized under "Driver support routines - process support) are...
PsSetCreateProcessNotifyRoutine - Monitors new process creation.
PsSetCreateThreadNotifyRoutine - Monitors new thread creation.
PsSetLoadImageNotifyRoutine - Monitors mapping of executable images (before execution) to virtual memory.
Here is my ASM code (skeleton process monitor)...
.386
.model flat,stdcall
option casemap:none
include \masm32\include\w2k\ntstatus.inc
include \masm32\include\w2k\ntddk.inc
include \masm32\include\w2k\ntoskrnl.inc
includelib \masm32\lib\w2k\ntoskrnl.lib
NotifyMe proto :HANDLE,:HANDLE,:BYTE
.data
pcreate db "Process is created",0
pexit db "Process is exiting",0
snotify db "Success: Notification routine registered successfully!",0
fnotify db "Error: Unable to register notification routine!",0
format db "%s:%d",0
.CODE
DriverEntry PROC pdrvobj:PDRIVER_OBJECT,pRegPath:PUNICODE_STRING
push 0
push offset NotifyMe
call PsSetCreateProcessNotifyRoutine
.IF eax == STATUS_SUCCESS
push offset snotify
call DbgPrint
.ELSE
push offset fnotify
call DbgPrint
.ENDIF
mov eax,STATUS_SUCCESS
ret
DriverEntry ENDP
NotifyMe proc ParentId:DWORD,ProcessId:DWORD,Create:BYTE
cmp Create,FALSE
jz lexit
push ProcessId
push offset pcreate
push offset format
call DbgPrint
jmp getout
lexit:
push ProcessId
push offset pexit
push offset format
call DbgPrint
getout:
ret
NotifyMe endp
END DriverEntry
Use the above code with MSDN documentation and it should be fine. Here is the gist anyway - Just register a notification routine and you will be notified every time a process is created at least with 1 thread (at least one thread will be there in most cases). There are new routines in later OS that wasn't there in Windows 2000. For example, in W2K it was required that the driver remains loaded until system is shutdown. Now we have options to Un-register the notify routines in case of thread and image load notifications. We are able to block the process creation too (documented functions) in later versions. With the protection of critical kernel data structures in later windows versions, such routines and facilities are important because earlier (say W2K times) we had to do other tricks to get the same task done. There are some "C" sample codes available online and especially in Malware related books. I didn't find an ASM sample (may be I didn't look enough). Anyway I wrote a few samples on above SPI. So it is quite simple. Below is the output, for the above sample process notification code, using Debug viewer utility.
That's it for today! :)

No comments:
Post a Comment